

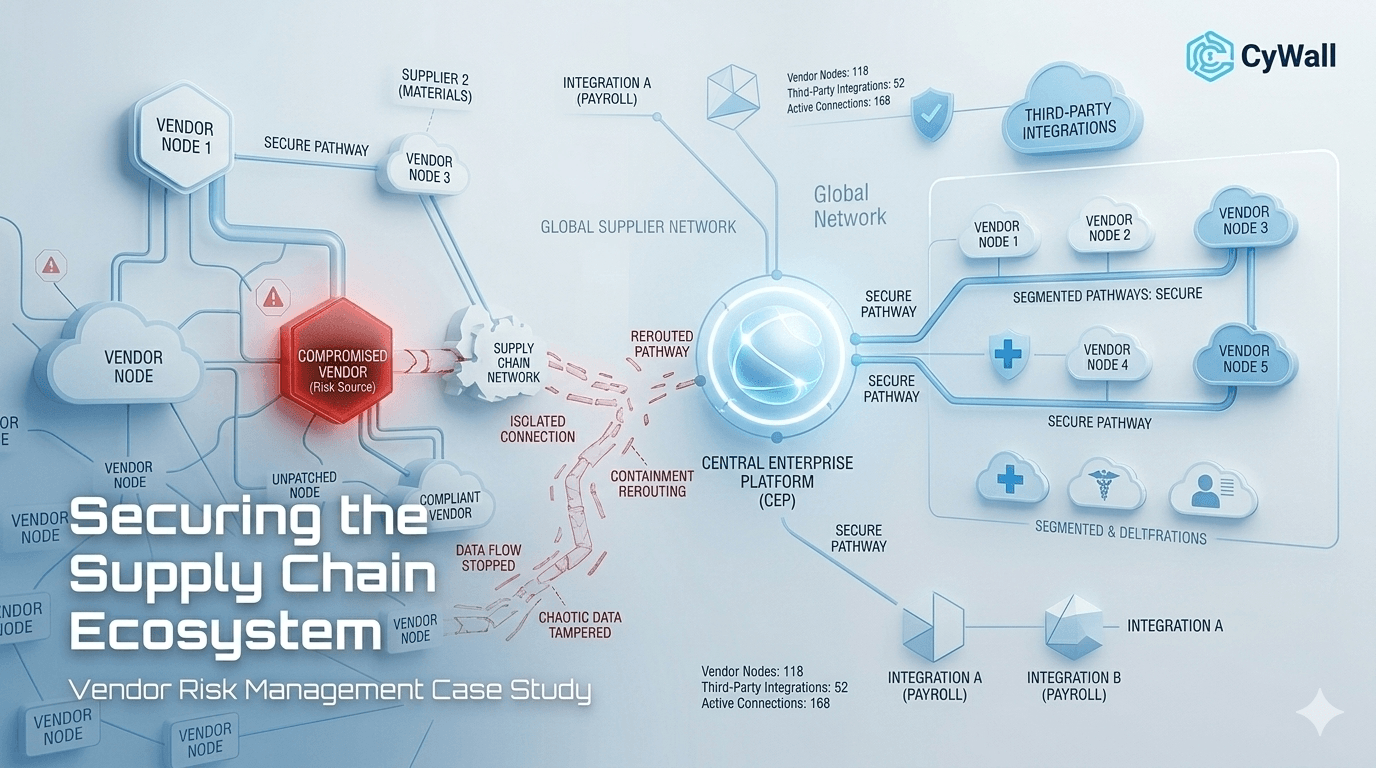
In late 2025, the “Clop” ransomware gang intensified attacks on third-party integrated software. Nexus Retail Group, which manages over 200 external vendors for logistics and payroll, realized they had no visibility into the security posture of these partners. Following a breach at one of their minor shipping partners, Cywall was commissioned to build a Vendor Risk Management (VRM) framework to prevent a “domino effect” breach during the high-traffic holiday season.
The "Holiday Rush" created a perfect storm for cyber-adversaries exploiting trusted connections.
Cywall executed a high-velocity "Zero-Trust Vendor Integration" project:


Attackers capitalized on the "Living Off Trusted Services" (LOTS) trend, where they used legitimate platforms like SharePoint and Oracle to hide malicious activity, making it nearly invisible to traditional firewalls.
No. Cywall utilized "Agentless Scanning" and secure browser-based gateways, ensuring the vendors remained compliant without needing to alter their own internal IT setups.
By enforcing micro-segmentation, even if a vendor is compromised, the attacker cannot "jump" from the vendor's system into the Nexus core network. The breach is effectively quarantined.
Absolutely. While this project was for an enterprise, the "Zero Trust" principles are scalable and essential for any business that shares data with even one external bookkeeper or SaaS provider.
Our framework includes a "Risk-Based Automated Response." If a vendor fails to patch a critical flaw within 48 hours, their access is automatically throttled or suspended until remediation is verified.

One stop solution for your security needs, designed to protect businesses from evolving digital threats.
51 Monroe St Suite, Rockville, USA
Copyright © 2026 All Rights Reserved.